Explaining the Dark Web
An Intro to Anonymity
Chances are, if you’ve heard the term “dark web” in the past few years, it’s conjured up horrific images of drugs, organized crime, and murder, to name a few. Contrary to popular belief, the dark web was not designed for criminal activity, and even today, that is not its only purpose, although operations like that do take place there. If you aren’t familiar with it, let’s clarify a few terms.
What Does “Dark Web” Mean?
According to Wikipedia, “the dark web is the World Wide Web content that exists on darknets: overlay networks that use the Internet but require specific software, configurations, or authorization to access.” Darknets are also sometimes referred to as “anonymity networks” because they obscure the identities of users on the networks.
The term dark web is often conflated with “deep web” in popular culture. As Techopedia defines it, “The deep web refers to any internet information or data that is inaccessible by a search engine and includes all web pages, websites, intranets, networks and online communities that are intentionally and/or unintentionally hidden, invisible or unreachable to search engine crawlers.”
Metaphorically, one might think of an office building. The “deep web” would be things inside the office building that people can’t see from the street. The “dark web,” on the other hand, would be things inside the same office building that required special keys for access, or that were hidden inside a vault that only managers could enter.
Anonymity Software
For the purpose of anonymity, there are a number of different types of software available, but one of the most popular ones is called Tor. Tor is acronym for The Onion Router. According to the Tor Project, its history began in the 1990s at the U.S. Naval Research Lab:
In the 1990s, the lack of security on the internet and its ability to be used for tracking and surveillance was becoming clear, and in 1995, David Goldschlag, Mike Reed, and Paul Syverson at the U.S. Naval Research Lab (NRL) asked themselves if there was a way to create internet connections that don't reveal who is talking to whom, even to someone monitoring the network. Their answer was to create and deploy the first research designs and prototypes of onion routing.
The purpose of onion routing was to help people use the internet with the maximum amount of privacy by sending traffic through a number of different servers, encrypting it along the path.
According to the Tor Project, “Tor began gaining popularity among activists and tech-savvy users interested in privacy, but it was still difficult for less-technically savvy people to use, so starting in 2005, development of tools beyond just the Tor proxy began.” In 2008, the project began development on the Tor Browser, which is a modified version of Firefox intended for anonymity and privacy.
When people think of the “dark web,” the Tor Browser is often what comes to mind, although that isn’t its only purpose. Tor, in the present day, refers to both the network (in the historical sense) and the browser (above). Users can host sites on the Tor network, known as “Tor hidden services” or “.onion sites,” which receive inbound traffic through the network to disguise their IP address and location.
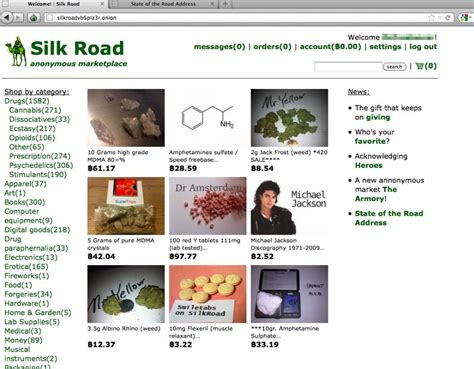
In 2011, American Ross Ulbricht founded one of the more notorious .onion sites, the Silk Road. The site was what’s known as a darknet market; according to Investopedia, darknet markets “…are dark web sites with goods for sale. Although some products for sale are legal, illicit goods such as drugs, stolen information, and weapons are common items in these markets.”
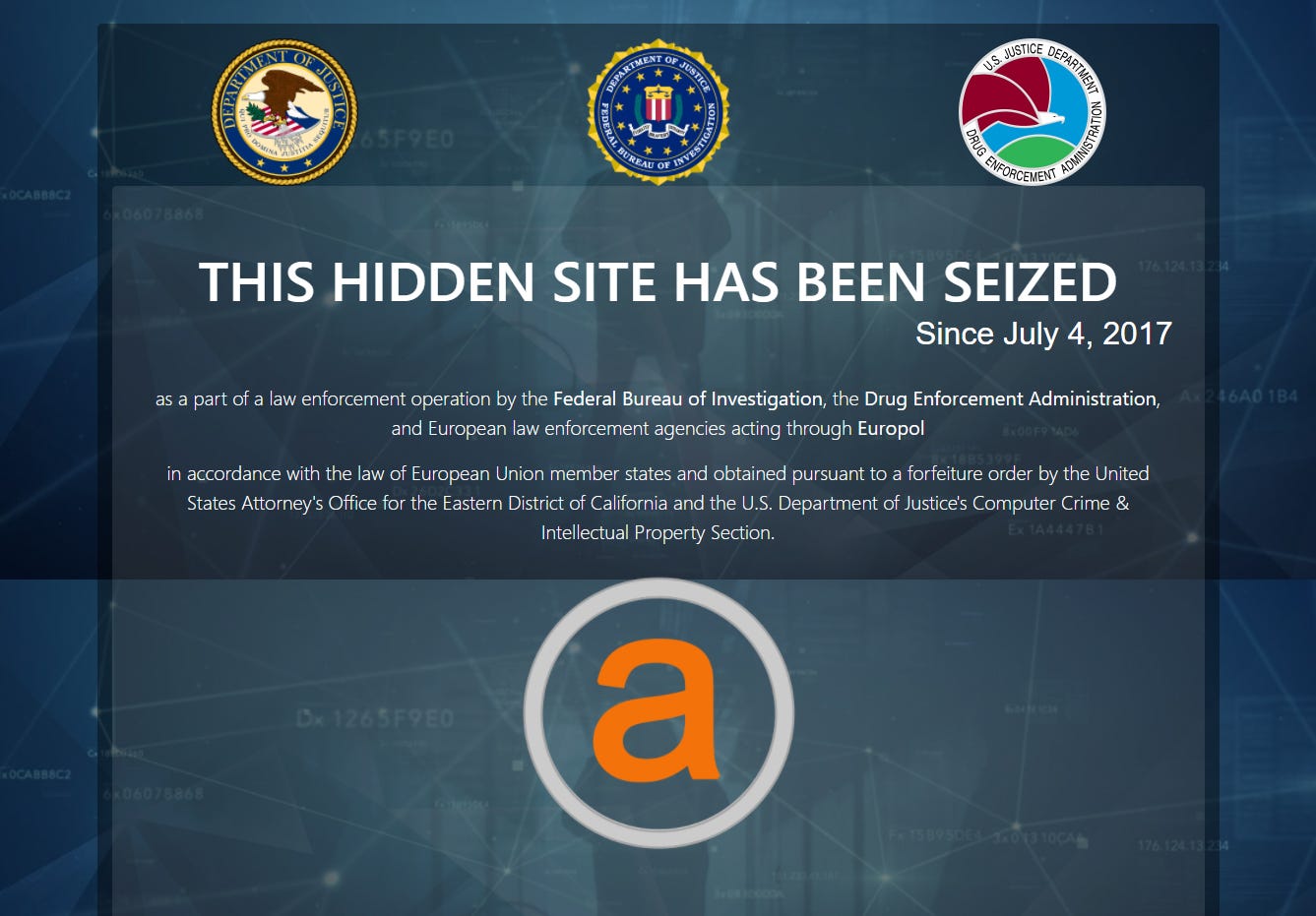
The Silk Road conducted transactions with the cryptocurrency bitcoin, which is still in use today by many darknet markets. Despite its seeming anonymity, law enforcement agencies such as the FBI and the Department of Homeland Security seized the site in 2013, leading to the arrest and indictment of Ulbricht and others connected with the site. Ulbricht received a life sentence. Other darknet markets eventually took the Silk Road’s place, such as AlphaBay and Hansa Market, though those sites faced the same fate as their predecessor.
Not all onion sites feature illegal activity, however. Many are forums, chat rooms, news sites, and sites where whistleblowers (like Edward Snowden) can share information without fear of giving away their true identities. Organizations like WikiLeaks, GlobaLeaks, and ProPublica operate onion sites for such reasons.
In the present day, even some well known organizations and publications have onion sites, like Facebook, the New York Times, and the CIA. Contrary to popular belief, it’s also possible to access the “clearnet” (the reciprocal term to “dark web”) through Tor.
I2P
Though less notorious than Tor, there are other types of anonymity networks that fall under the umbrella of “dark web.” One of these is I2P (an acronym for “Invisible Internet Project”). According to Techopedia:
I2P is an open-source free technology. Many applications, such as mail, IRC chat, peer-to-peer applications, file sharing and instant messenger, use [the] I2P interface to allow anonymous communication and operation for both the individual users and organizations. I2P possesses its own internal network database, which is used to distribute contact and routing information in a [secure network].
I2P is known as an anonymous peer-to-peer (P2P) network built using Java, in which the users are anonymous or pseudonymous by default. Such networks are often used for filesharing and evading censorship. I2P also allows users to host websites, though unlike Tor, it does not have an official browser. Rather, it can be used in standard browsers like Firefox and Chrome through a proxy server. As opposed to using Tor, I2P requires more manual configuration and is geared toward more advanced users.
For example, once the I2P software is installed and someone is connected to the network, they can open a browser, such as Firefox. In Firefox’s Network Settings, they can change the “HTTP Proxy” under “Manual Proxy Configuration” to Port 4444. After this, they must go to the address about:config and find the property media.peerConnection.ice.proxy_only, and change this setting to “True.”
When this is set, they can then access I2P websites, also known as “eepsites.” For instance, I2P has its own email service, called I2P Mail, designed for extra privacy and anonymity, at the address hq.postman.i2p. Unlike a service such as Gmail, in I2P Mail, you can only send messages between yourself and others who are running I2P Mail.
I2P is also popular for such things as filesharing; one of the applications used for this is called I2PSnark. Files such as videos, images, music, and software are often shared over this service.
While Tor can be used for filesharing as well, most don’t recommend doing so, as it slows down the network, and can also compromise anonymity. The reason for the latter is that when someone connects to an outside application for filesharing, such as BitTorrent, that can potentially reveal the person’s true IP address.
Freenet
Freenet, like I2P, is also an anonymous P2P network; similarly, it can be run in any browser. In terms of its use case, Freenet is geared toward censorship-resistant, anonymous publishing and website hosting. Like I2P, it is also used for filesharing. Its software can be downloaded from The Freenet Project.
In a similar fashion to Tor’s .onion sites and I2P’s eepsites, users can publish what are called “freesites,” which are sites hosted inside the Freenet network. Freesites, as opposed to onion and eepsites, use what are called URIs (Uniform Resource Identifiers) instead of URLs. Freenet URIs contain part of the site’s public cryptographic key to “…guarantee the integrity of retrieved data,” according to Freenet’s documentation. As with I2P, Freenet has its own privacy-oriented email, messaging, and forum software, and even a social network akin to Facebook, called Sone.
One major difference between Freenet and the other anonymity networks is that it includes what’s called a datastore. Users of Freenet can designate part of their hard drive to share files on the network, which helps add to the censorship resistance feature. In essence, freesites aren’t hosted under any one hosting provider, and thus they become more difficult to seize (as has been the case with many Tor sites).
Freenet also features what is referred to as a “darknet mode,” in which you only connect to friends that you trust. This type of feature is especially helpful for people such as whistleblowers whose lives may be in danger for publishing or sharing controversial material. For example, Freenet has a mirror of Wikileaks (though it isn’t the most up-to-date), in case the clearnet site is taken down by authorities, and also has free PDF copies of contentious literature.
Additionally, because some eBooks use Digital Rights Management (DRM) to prevent them from being downloaded for free, there are freesites that specialize in downloadable eBooks, such as “Bookworm’s Library.”
Red Rooms
There are many persistent urban legends surrounding the dark web in general, one of which is the idea of “red rooms.” According to the legend, in a red room, someone can pay to watch another person be tortured or murdered on a live video for bitcoin. On Tor, in particular, there are numerous scam red rooms claiming to offer this service, but thus far, none have been proven to be genuine.
In the case of Tor, it is particularly difficult to stream video, because of the onion routing method that Tor uses for anonymity. Most content has a tendency to load slowly, in particular videos and anything that requires a lot of bandwidth. In addition, most sites on which you can watch videos require JavaScript or other scripts to be enabled, which can potentially reveal your IP address or other identifying information.
There have been many other types of scam sites as well, such as those offering assassination services or bitcoin stealing scams, so it is reasonable to assume that the red rooms are scams as well.
Why Use Them?
Anonymity tools like Tor, I2P, and Freenet are important, despite the fact that they are sometimes used for illegal activity. People who need the ability to speak out without endangering their lives rely on such software in order to have the freedom of speech that is sometimes taken for granted in other countries.
Plus, these types of networks allow citizens to circumvent censorship and government oppression in many areas of the world. As illustrated on Turkey Blocks, for example, the country often blocks services like Periscope, Facebook, and AliExpress, to name a few. The anonymity tools outlined here often give people a way around these censorship efforts.
Tools like these will continue to exist, regardless of whether authorities try to take them down or not. In fact, there will likely be other such types of software in the future.